
Why RebelMouse Is the Most Secure CMS on the Web
Delivering a secure, high-performing environment with extreme reliability is essential to all of our clients at RebelMouse. We only use industry-leading, reliable approaches to host our infrastructure. This ensures maximum stability and security for all of our clients’ data. Here are just some of the reasons we’re able to maintain a hard-bodied product that’s flexible, too.
Inside the Most Secure CMS of 2024
- Why RebelMouse Is More Secure Than WordPress
- WordPress Was Built for a Blogger in Their Pajamas. RebelMouse Is Built for High-Value Websites That Are Stable.
- Stability and Around-the-Clock Support
- Web Application Firewall
- Bug Bounty Program
- A Full List of What Makes RebelMouse the Most Secure CMS
- Publish on the Most Secure CMS on the Web
Why RebelMouse Is More Secure Than WordPress
We’ve spent years building the most secure CMS of 2024. Open-source CMS platforms like WordPress and Drupal mean everyone has access to your code, and that means your website is completely vulnerable.
Think about it: There are millions of instances of WordPress in the world, and every security update and feature upgrade — no matter how big or small — has to be manually performed for each individual site to avoid outright breaking custom code, plugins, and more. On WordPress, you need a plugin to manage simple things, but those seemingly safe tasks can put your entire site at risk. For example, a plugin to manage affiliate links gave hackers an easy opening to add their own links instead.
Examples like these leave open-source CMS options like WordPress constantly vulnerable to security threats. If you are running a real online business, easily exposed features like plugins are a 2005-era feature that now serve as a major weakness on your site. Security threats created by outdated plugins can put hundreds of thousands of sites at risk, like this breach in 2022 that threatened the safety of 600,000 sites.
More recently, approximately five million WordPress sites were updated to resolve a significant vulnerability introduced back in 2012. Jetpack, a WordPress plugin developed and maintained by Automattic, offers a range of security safeguards and is among the most widely used plugins for the WordPress content management system.
In May 2023, Automattic made an official announcement regarding the rollout of a critical security update. This update addresses a vulnerability that affects all versions of the Jetpack plugin since its release of version 2.0. These constant, sudden spikes in attacks have no end sight, and here's why.
Never Worry About Stability Again. Unlock Hacker-Proof Publishing.
Click HereWordPress Was Built for a Blogger in Their Pajamas. RebelMouse Is Built for High-Value Websites That Are Stable.
Every time a WordPress security breach is announced, the proper updates have to be made one by one. This is because the only way WordPress core developers can patch significant flaws within their software is to deploy fixes to users in the form of user-installed product updates.
In fact, WordPress announced that versions 3.7 through 4.0 will no longer receive security updates beginning on December 1, 2022. That's because the task of keeping every version up to the date is too burdensome.
This isn't an issue on RebelMouse. All of our updates are quickly deployed at once to every site we power. We often deploy multiple updates on a daily basis. While many WordPress users count on third-party hosting companies or in-house developers to stay on top of the platform’s updates, RebelMouse users can rest easy knowing that important updates are taken care of immediately.
RebelMouse isn’t a solution for cheap websites. We’re a solution for high-value websites that are high-performing and highly secure. It’s also why we’re able to power some of the fastest sites on the web with superior scores on Google’s Core Web Vitals. Click here to learn more.
Transparency is a priority. The sites in our network subscribe to a status portal that provides up-to-date details on platform performance with real-time updates.
Stability and Around-the-Clock Support
We only use modern and reliable approaches to host our infrastructure for maximum stability. We host our infrastructure in the Amazon Web Services (AWS) cloud because AWS is the most trusted, secure, and reliable infrastructure in the world. We have great relationships with the folks at AWS and utilize the best of their services.
All of our production services are covered with AWS Auto Scaling groups, which means we can sleep at night without worrying that something may go wrong. Our services are self-healing 24/7 as well. And even our stateful services, like databases, are covered with reliable automatic failover and backup solutions.
Since the RebelMouse team spans dozens of countries, we offer 24/7 live support. This means that any vulnerabilities that pop up will never be left unattended. In fact, many updates and patches are deployed across our platform in seconds without any interruption to our site network at all.
Click here to learn more about RebelMouse’s infrastructure.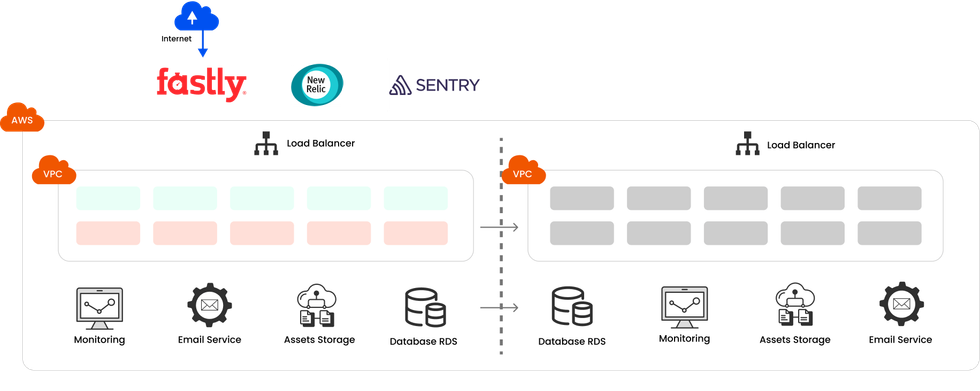
RebelMouse delivers 99.99% uptime with maximum performance, stability, and security.
Web Application Firewall
AWS's Web Application Firewall (WAF) is a firewall that helps protect your web applications (or APIs) against common web exploits that may affect availability, compromise security, or consume excessive resources. AWS WAF gives RebelMouse developers control over how traffic reaches our applications by enabling us to create security rules that block common attack patterns, such as SQL injections or cross-site scripting (XSS), and rules that filter out specific traffic patterns we have defined. These rules are regularly updated when new issues emerge as well.
With AWS WAF, we're making sure that all of our sites are covered against some of the most common attacks, as defined by The Open Web Application Security Project (OWASP). The project is an online community that creates freely available articles, methodologies, documentation, tools, and technologies in the field of web application security.
Click here to learn more about WAF.
Bug Bounty Program
To strengthen our commitment to security, RebelMouse offers a bug bounty program. If you believe you've found a security issue on our site, or any of the sites we power, we may compensate you for your discovery. We look at all submitted reports, and if we agree that it's a valid finding, we'll pay $250 for each one.
Click here for more information about what qualifies as a security vulnerability and how to report a bug.
A Full List of What Makes RebelMouse the Most Secure CMS
Amazon Web Services (AWS)
- RebelMouse uses the following services that are compliant with SOC 1, 2, and 3:
- API Gateway
- CloudFront
- CloudWatch
- DocumentDB (with MongoDB compatibility)
- EC2 Container Registry (ECR)
- Elastic Compute Cloud
- Elastic Container Service for Kubernetes
- Elastic File System
- ElastiCache
- Key Management Service
- Lambda
- Relational Database Service
- Route 53
- Simple Email Service
- Simple Notification Service
- Simple Queue Service
- Simple Storage Service
- RebelMouse uses the following AWS security, identity, and compliance services:
- Identity and Access Management
- AWS Identity and Access Management (IAM) (for access control of users)
- Threat Detection and Continuous Monitoring
- AWS CloudTrail (for tracking users’ activity)
- AWS Trusted Advisor (for general audition)
- Infrastructure Protection
- VPC
- Private Networks
- Security Groups
- Firewall
- VPC
- Data Protection
- Compliance and Data Privacy
- AWS Artifact (for access to compliance reports)
- Identity and Access Management
Fastly
Fastly’s CDN is certified under the Swiss-US framework. We use the following Fastly services:
- DDOS Mitigation
- Edge Filtering
- Origin Cloaking
- Rapid Response
- TLS Encryption
Click here to learn more about our Fastly recovery plan.
Password Management
- We use 1Password to manage all logins across the company.
- Two-factor authentication through major third party applications, including Google.
SOC 2 Certification
SOC 2 certification is critical to building trust with customers. It's not just a stamp of approval. It's a powerful signal that RebelMouse takes data security seriously; we are meeting compliance requirements and gaining a competitive edge by demonstrating a commitment to customer privacy, robust risk management, and continuous improvement. SOC 2 is a gateway to building solid and lasting relationships with clients who demand data protection. RebelMouse is proud to be SOC 2 compliant and deliver the highest level of security on the web to our customers.
Publish on the Most Secure CMS on the Web
A lot of publishers may think uncertainty in the digital space means it’s time to double down on in-house developers to create a site experience that stands out against the noise. But it's actually the opposite: It’s time to invest in an external team that creates and manages tech for you, so you can instead focus on creating content that resonates with new and existing audiences.
Our infrastructure summary may come across as Greek to you, but that’s all right. Let’s create something together that isn’t just powered by next-level strategies, but also innovative and stable technology. Your content will be both protected and optimized for long-term growth.
Request a proposal today and let’s start working together.










































































